The Internet is a crucial tool in redefining and promoting businesses. But unfortunately, it has become a malicious tool for cybercriminals to carry out unsuspecting fraud targeted at companies and organizations. Understanding how these crimes are executed will go a long way in helping companies and organizations arm themselves properly. One such crime is Business Email Compromise.
What is a Business Email Compromise (BEC)?
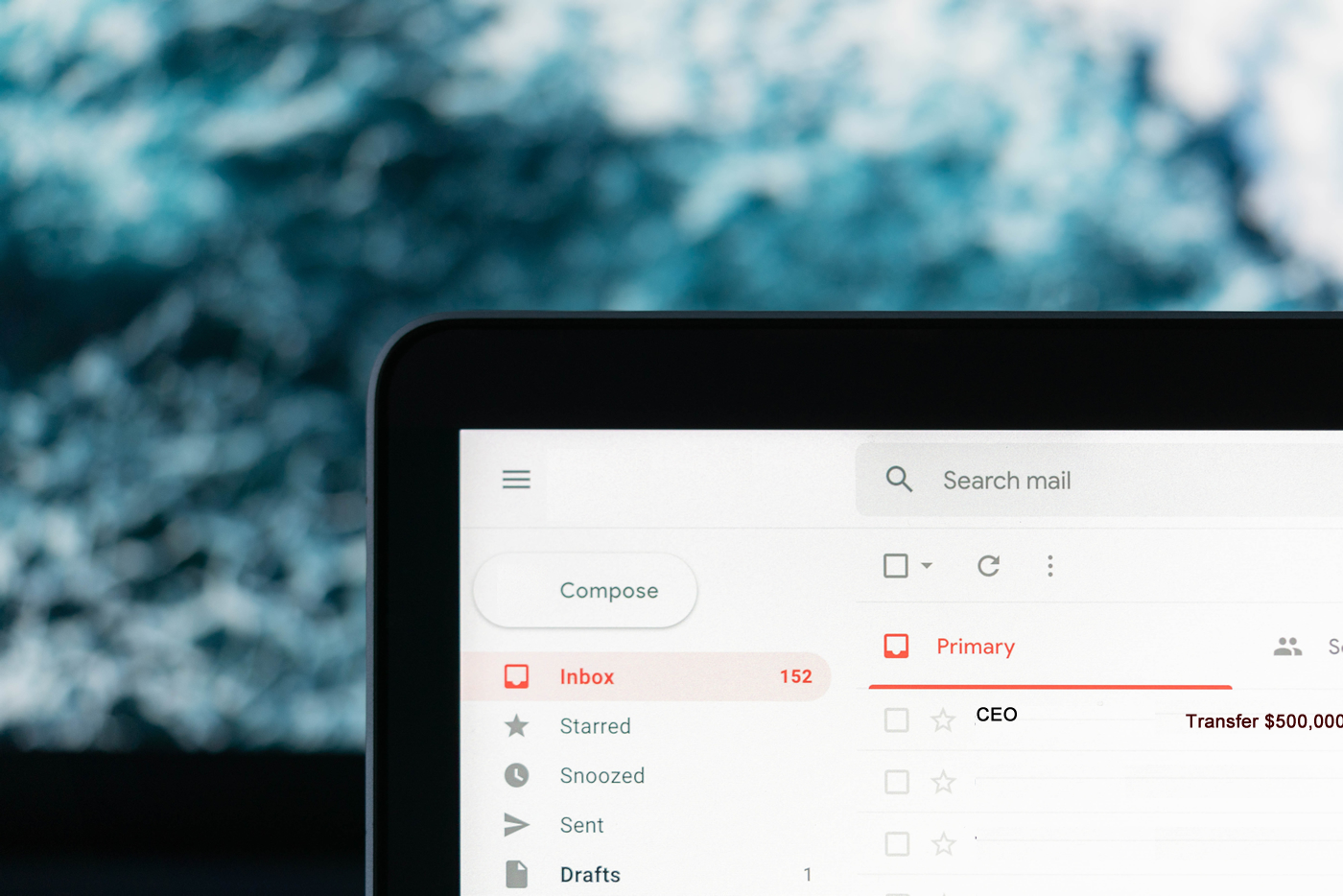
Business Email Compromise (BEC) is a kind of email cybercrime in which the perpetrator targets an organization to defraud it, especially organizations that conduct wire transfers. It is also known as Email Account Compromise (EAC) and was initially known as Man in the Mail Scam. A business email compromise is a rising issue that calls for serious attention. It has become a concern because it is one of the most financially damaging online crimes.
How it Works
The email address of an executive or a high-level staff member associated with finance or wire transfer payments is either falsified or compromised via key loggers or phishing tactics.
The attacker in a BEC scam presents himself as someone the victim should trust, such as a vendor, coworker or manager. The attacker impersonates an executive and instructs the unsuspecting victim to initiate a wire transfer to an account the attacker would provide
Most times, BEC operations don’t utilize malware or deceptive URLs, which common cyber defences can evaluate. Instead, BEC assaults use mimicry and other social manipulation strategies. Manually analyzing and remediating these assaults is tough and time-wasting due to the sophisticated social engineering skills of the attackers.
Summarily, it works in the following sequence:
- Email List Targeting: Identifying target emails, websites and valuable information.
- Launch Attacks: Launch a phishing attack to access victims’ emails.
- Social Engineering: This is the impersonation phase.
- Financial Gain: A financial transaction happens after building trust.
Notable Victims of BEC Scams
BEC Scams usually target mainstream organizations. However, sects, religious establishments, non-governmental organizations, and governmental organizations are not excluded. Take a look at some victims of the BEC scam:
- Toyota 2019: In 2019, Toyota Boshoku Corporation, a Japanese automotive component supplier, was the victim of a USD 37 million BEC fraud. An executive in the corporation’s economic department was fooled and induced to execute a wire transfer.
- Pathé 2018: In 2018, Pathé, a French film company, was the victim of a BEC scam that cost EUR 19 million. The perpetrators appeared to have used an email address with the domain pathe.com to imitate the organization’s CEO in France.
- Ubiquiti Networks 2015: In 2015, Ubiquiti Networks, a technology-based business organization, was hit by a BEC attack and lost USD 46 million.
- St. Ambrose Catholic Parish 2019: In 2019, Crooks sent messages to the St. Ambrose Catholic Parish in the United States. They claimed to be specialists and hadn’t been paid in months. They convinced the church authorities to wire USD 1.7 million to a fake account.
- Facebook and Google: A BEC assault on tech goliaths Facebook and Google set both companies back with $121 million. The fraud occurred between 2013 and 2015. Evaldas Rimasauskas, the perpetrator, was condemned to five years in jail in 2019.
How to Protect Yourself against BEC Scams
To every problem, there’s always a solution to proffer. The utmost care and attention to detail are the basics of protecting yourself against BEC Scams. Organizations can implement a few procedures to defend themselves from Business Email Compromise.
- Intrusion Detection System Rules: This technique helps identify email campaigns with plug-ins similar to company emails. Carefully look at the following samples: A genuine email from abc_edu.com, for instance, would alert a fake email from ABC-edu.com.
- Email Rules: This technique alerts a difference between the “reply” and the “from” email addresses.
- Colour Coding: This technique ensures messages from representative/inner records come in one colour, while announcements from non-worker/outer records appear in another colour.
- Payment Verification: This technique ensures using a two-factor authentication code to carry out transactions to increase security.
- Careful Scrutiny: This sums up everything, as earlier mentioned. Detailed and thorough observations should be carried out on suspected emails.

Chiedu Ogobueze
I oversee the effective utilization of technology in businesses and organizations. I design, manage, and protect information systems.